Table of Contents
Better organization of secrets
Better Data & Business Protection With This Password Manager – Today’s Internet services rely heavily on text passwords to authenticate users. The prevalence of these services, along with the difficulty of remembering large numbers and symbols of secure passwords, lead users to reuse simple, easily-guessed passwords across multiple websites, making their accounts vulnerable.
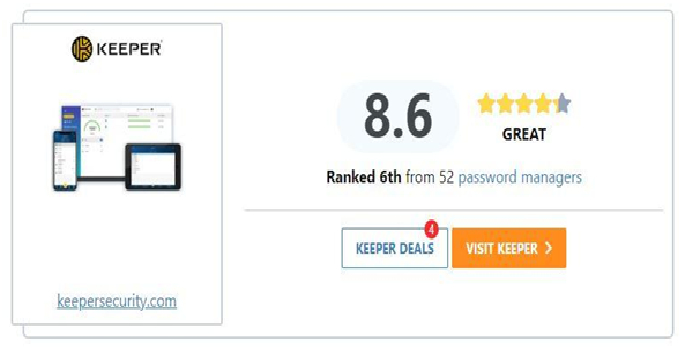
We always recommend that you use a password manager – it allows you to not only use strong, complicated passwords that you don’t have to type in manually but also to easily use unique passwords for network accounts.
Password Manager is an open-source application that helps you securely manage passwords. You can put all passwords in a single database that is locked with a single master key or key file, or both.
Organize passwords into groups or bookmarks. The number of passwords that a user has to remember continues to grow, and it is estimated that a typical Internet user has more than twenty different accounts online. As you add more and more accounts, your passwords will become more and more irresistible to manage. Password Manager allows you to organize passwords into groups or bookmarks. You can add as many groups as you need and use them to organize all your applications in any order that makes sense to you.
Password Manager has several other benefits. Automatic filling of queries or files, the user interface is very easy to use and use, possible synchronization with other devices.
Protection of privacy and data on the Internet
Any personal information that can be linked to you online enters your digital fingerprint. Your data that you leave on social networks – name, surname, place of residence, the school you attend, your interests, photos and videos, comments you write below the content that others post. The digital footprint is your trace in the digital world. Unlike the real world, this trace is almost impossible to erase.
When opening a profile on new social networks, it is not necessary to leave all the information, no matter what we are asked to do. There are those obligatory data such as name and surname, but also those that are not obligatory and which should never be left, such as telephone number, residential address, the school you attend.

Cookies are small files that are located on the sites you visit, and they collect information about which articles you read, which content you search. Then when you return to that page one day, the content will be tailored to your interests. This is not so bad, because interesting content is available to you without much searching. However, this in a way violates your privacy, that is, the freedom to decide what you want. What’s good is that we can manage cookies ourselves. To prevent our data from being collected by a third party that may “invade” the page or site you are reading, you can find the “cookies” option in the browser’s privacy settings, and then “block third-party cookies”.
Who is in charge of privacy?
All of us. We are the ones who create the content. We are the ones who need to know how to protect our own and other people’s privacy, how to recognize dangerous situations, and ways to stay away from them.

When you are at home, pay attention to whether someone is connected to your home internet, especially if it is wireless, because there is a possibility that someone will intercept your data. You have to put a password on your wi-fi. Also, when you are away from home and connect to any open network, wi-fi, and log in to any of your social media profiles, you are exposed to your data falling into the hands of hackers or people with no good intentions.
We tend to open several “tabs” (tabs or windows) while using the Internet. If we have an open e-mail, an account on the social network, among the tabs, we run the risk that other open pages will collect our data. Therefore, the advice is to log out and continue surfing the Internet.
Protection and security of electronic business
The Internet is an open network, whose structure and protocols do not provide enough security, and cybercrime is becoming an increasingly important problem, both for organizations and individuals. Not every form of cybercrime is directly linked to money – in some cases, the goal is only to disrupt or block a website, not to directly steal money, goods and services. Cybercrime against e-business is dynamic and changing all the time, with almost daily new risks and forms of attacks, so managers must be well prepared and follow the latest developments in security systems and techniques. Threats often come as part of downloaded files from the Internet and this is now one of the most common ways to infect a computer. Operating system security enhancements: The most obvious way to protect servers and clients is to take advantage of automatic security system updates.
MORE INFO:- tipsformart


